The ISO 27001 Family of Documents
- ISO/IEC 27001
- ISO/IEC 27002
- ISO/IEC 27003
- ISO/IEC 27004
- ISO/IEC 27005
- ISO/IEC 27006
- ISO/IEC 27007
- Requirements
- Code of practice for controls
- Implementation guidelines
- Measurement
- Risk Management
- Requirements for 3rd party audit and certification
- Overview and Vocabulary
The full range of the ISO 27000 family of standards goes up to ISO/IC 27043
While ISO/IEC 27001 and ISO 27006 are requirements standards, the remainder are essentially guidelines or best practices.
ISO/IEC 27001:2022 Requirements Structure and Security Categories
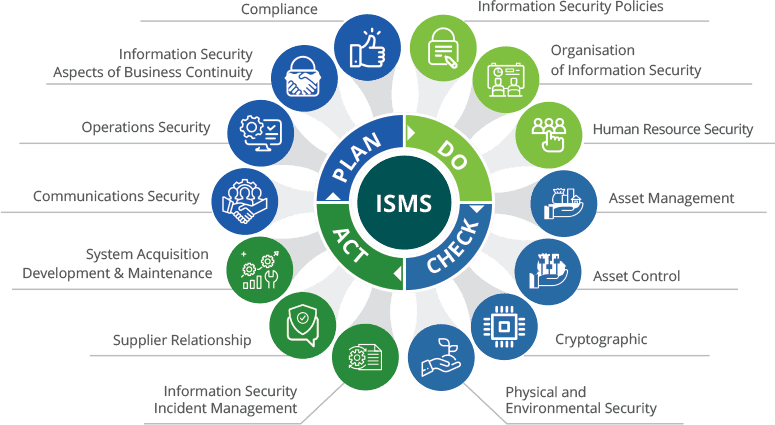
Annex A is comprised of security control clauses or “security domains”, Security categories, or “control objectives” and controls.
Controls are typically selected from Annex A (or equivalent control structures) based on risk assessment, risk treat-ment, legal, contractual, or regulatory requirements (NIST 800-171) or based on best practices.
What is NIST SP 800 Series?
The NIST SP 800 series is a set of documents managed by NIST (National Institute of Standards and Technology). Containing more than 160 documents, the NIST SP 800 series provides guidelines for the implementation of computer security policies, procedures, and configurations, such as:
What is NIST SP 800 Series?
- The NIST SP 800 series is recommended for organizations that are highly dependent on computer environments, and for those required to provide a stable and trustworthy computing environment.
- These documents provide both nonspecific and non-technology-oriented practices, as well as recommendations for specific technologies, and like COBIT and ISO 27001, can be used by organizations of all sizes, from both the private and public sectors.
- The main disadvantages of the NIST SP 800 series are related to the lack of centralized documents to help beginners to have a systemic overview of the material, and the fact that the documents do not cover integration with management practices or with other organizational processes.
A document that provides a methodology to implement information security in an organization’s cyber environment, making it easier to identify and use all other documents from the SP 800 series.
NIST SP 800 Series Key Takeaways
Similarities:
NIST SP 800 process-related documents provide method-ologies for how to implement the frameworks in practice, while ISO 27001 already has proven implementation methodologies available in the market. Although their steps are not 100% aligned, minor adaptations can easily narrow the gaps (see next section for detailed information)
Process-oriented:
NIST SP 800 process-related documents make use of a process approach to organize the activities, and this can be used to form a systemic view of how they can interact.
Security implantation based on risk management:
NIST 800 series adopts a risk management approach to define which security controls and safeguards should be applicable
Technology neutrality on processes:
Considering processes, all three approaches rely on general concepts, in both information technology and information security, which gives organizations the freedom to adopt the technologies most suitable for their environments

Integrated Management Systems
Integrated Management Systems (IMS) is the integration of QMS (Quality Management System), EMS (Environment Management System), OH&S (Occupational Health and Safety), ISMS (Information Security Management System), Social Responsibility and other regulations / standards and requirements into a single management system.

Omnex Methodologies and Practices
Omnex core strengths are spelled out in the 16 methodologies in which we specialize. Each of these practices are best in Class practices that can be implemented based on the needs of a specific organization in any industry.
How Can We Help You
For any service request or to seek consulting, Our Customer Service Team is ready to serve you, round the clock.

 Aerospace
Aerospace 



